GET CLEARER UNDERSTANDING OF POTENTIAL ATTACKS
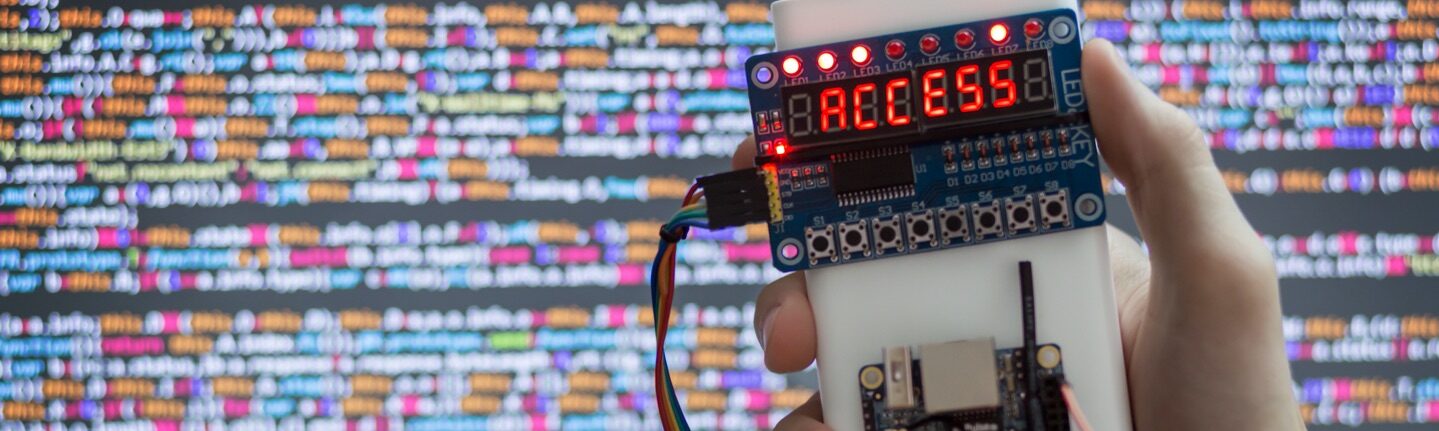
Incenter employs cutting-edge exploitation techniques to simulate real-world attacks, giving you a clear understanding of how an attacker could potentially compromise your systems and access sensitive data.
By replicating the tactics, techniques, and procedures (TTPs) used by actual threat actors, Incenter provides a realistic assessment of your security defenses and helps you identify areas where improvements are needed.
Incenter’s continuous penetration testing solution employs the latest attack techniques and methodologies to uncover vulnerabilities that conventional testing methods might miss.
By staying abreast of the latest developments in the cybersecurity landscape, Incenter ensures that your organization’s security posture is thoroughly assessed against emerging threats.
Incenter’s knowledge enables your security team to develop effective countermeasures and safeguards, ultimately strengthening your organization’s overall security posture.
